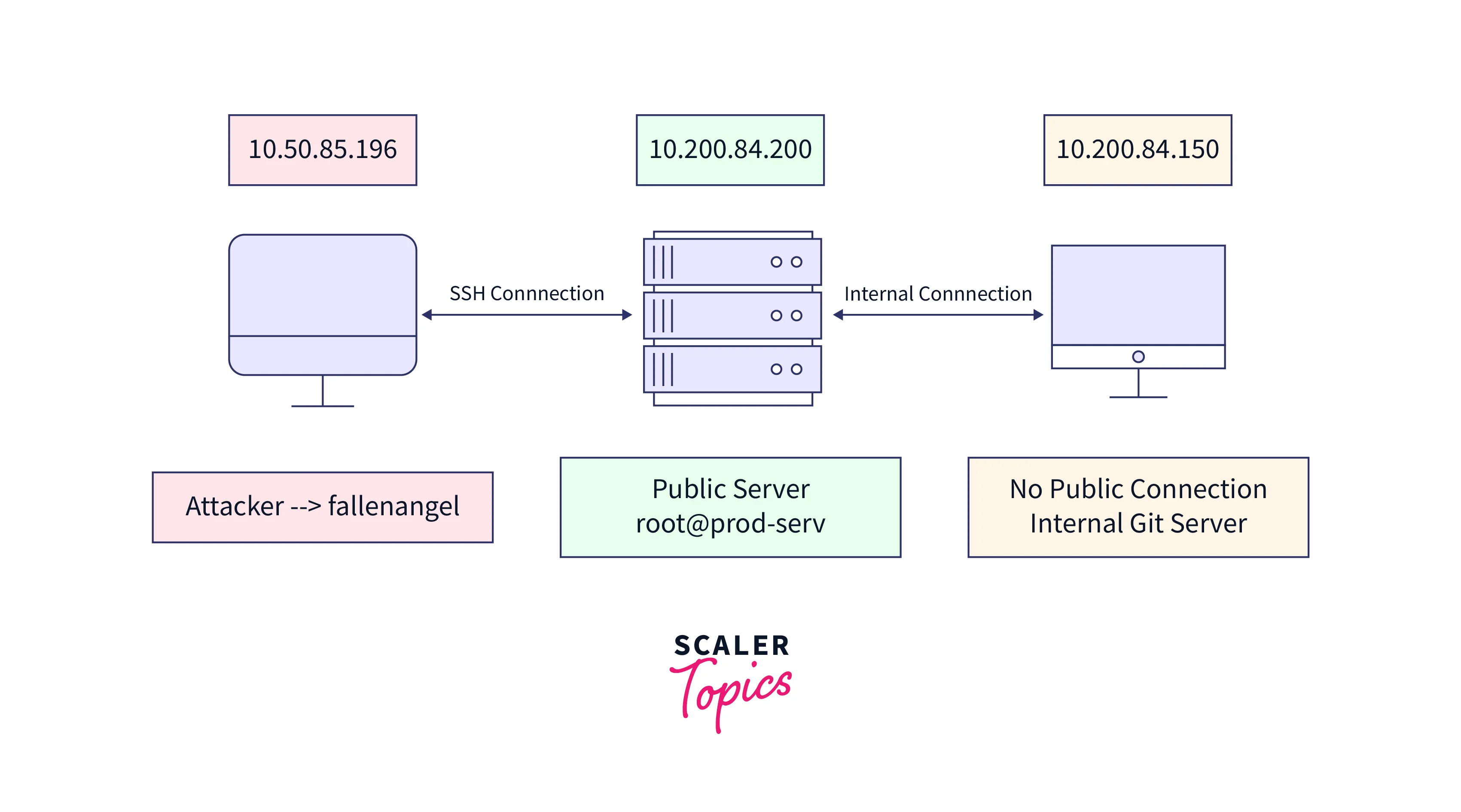
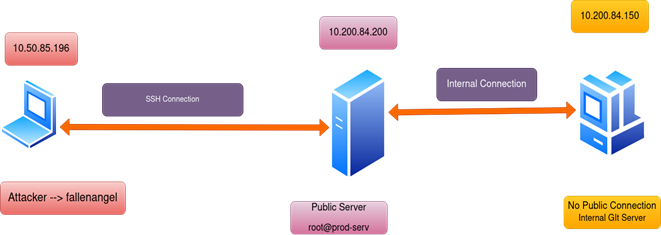
The Art of Network Pivoting and Lateral Movement: 9798851204463: Luberisse, Josh: Books - Amazon.com

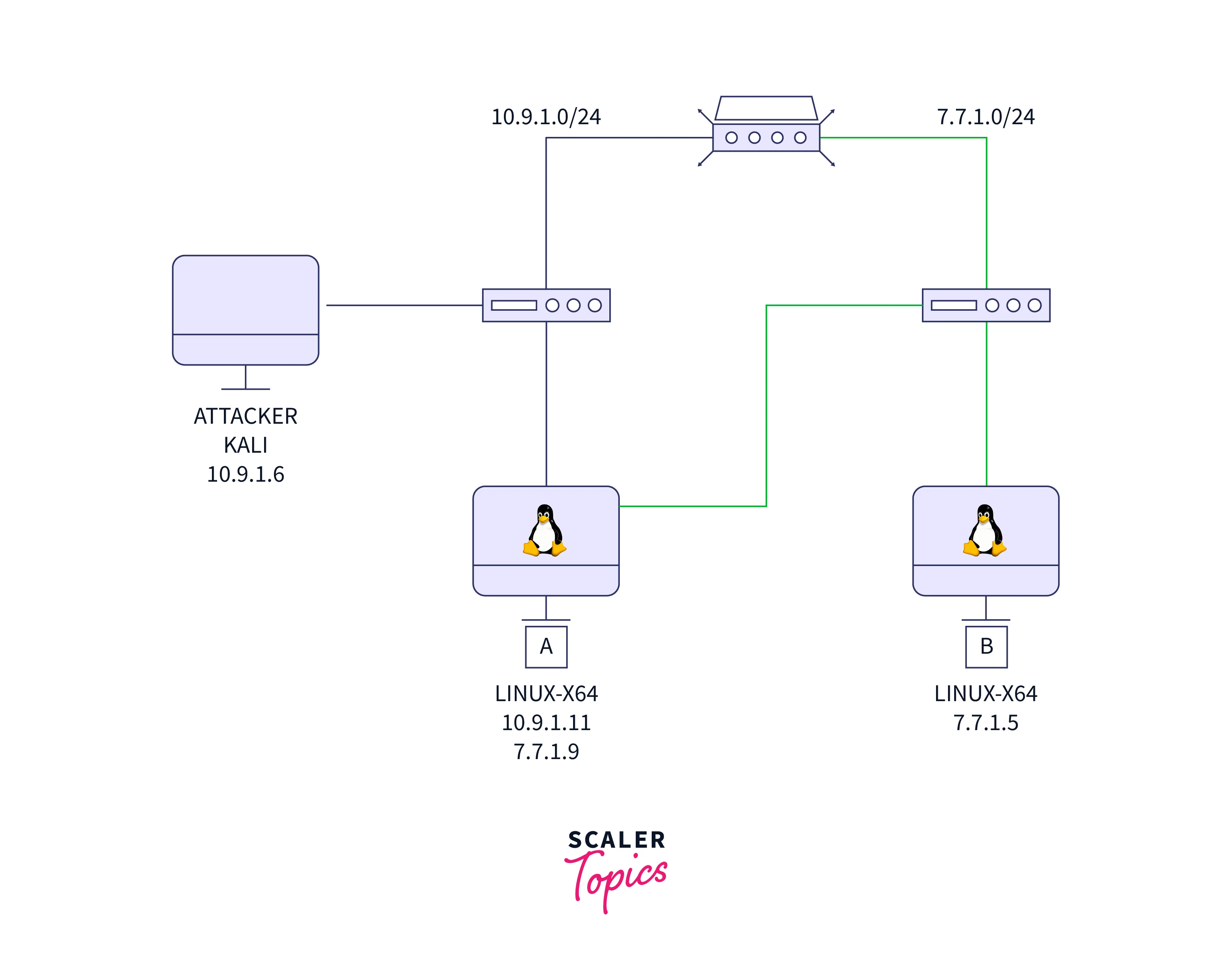
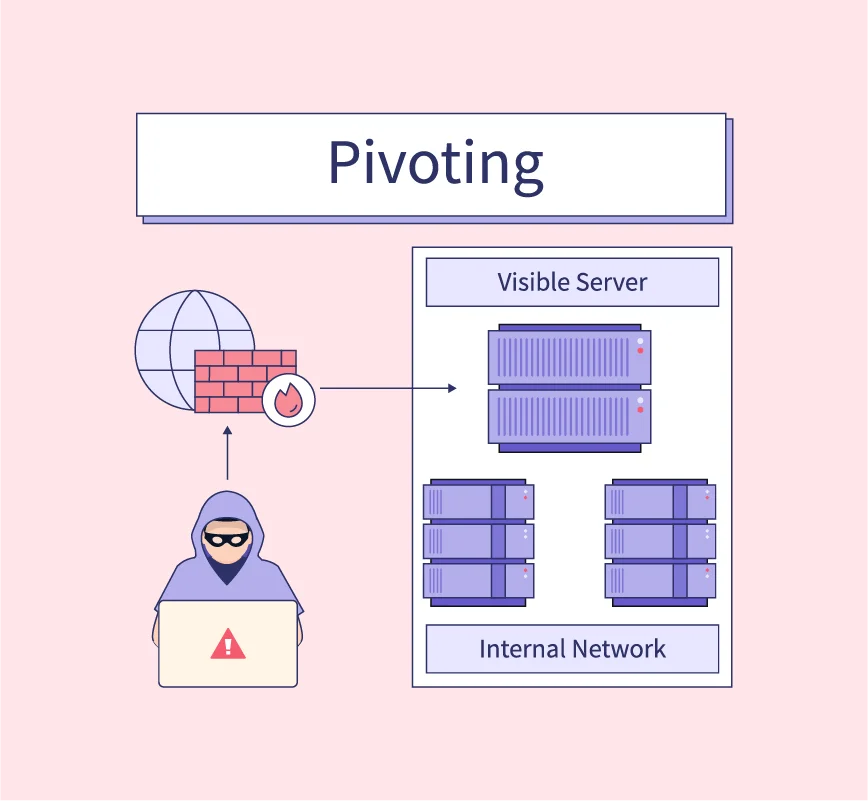
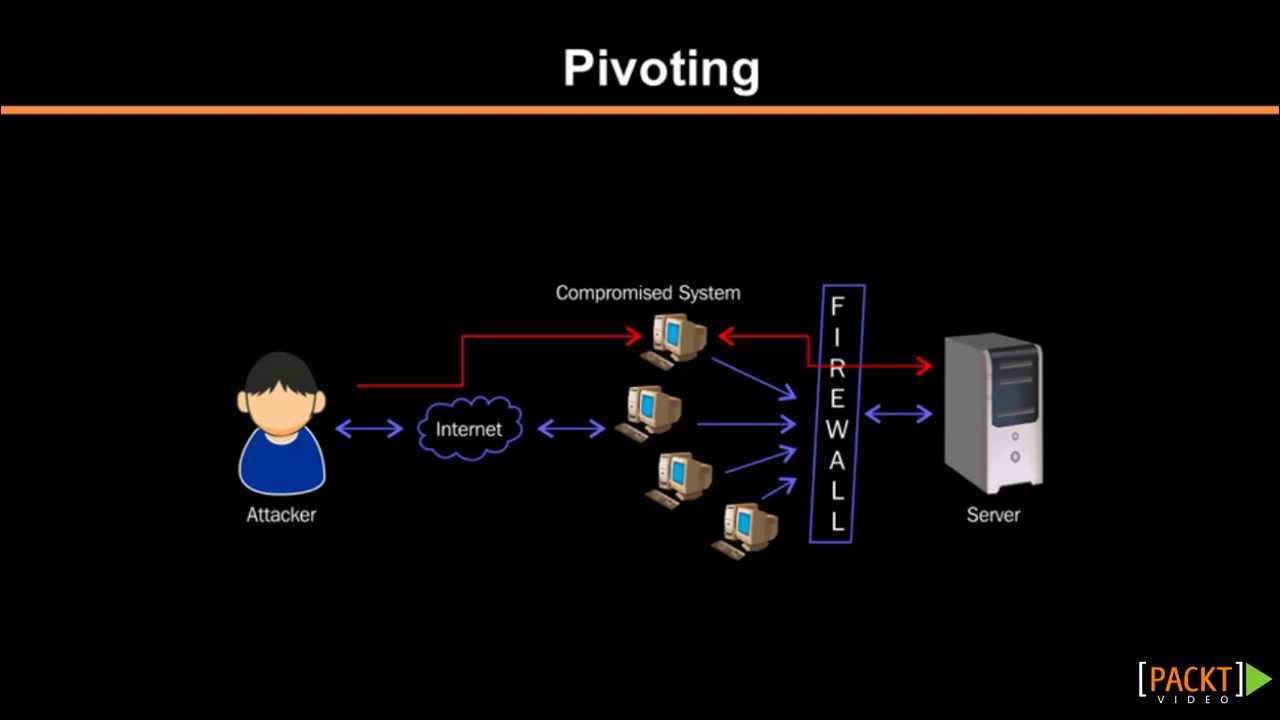
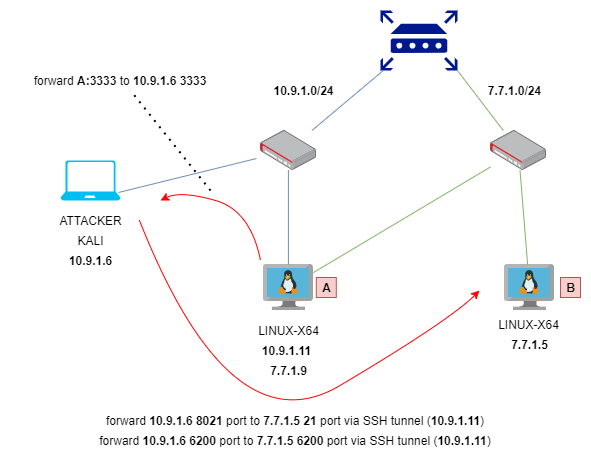
Hack3rScr0lls on X: "Looking for a stable reverse proxy for pivoting? Check frp! Useful when you've hacked a server and want to establish a channel to the internal network. A lot of